What's the deal with encryption strength —is 128 bit encryption enough or do you need more? | by Lance Gutteridge | Medium

How Secret Recovery Phrases Work. Understand the mystical secret words… | by Ernesto Ojeda | Neftify | Medium
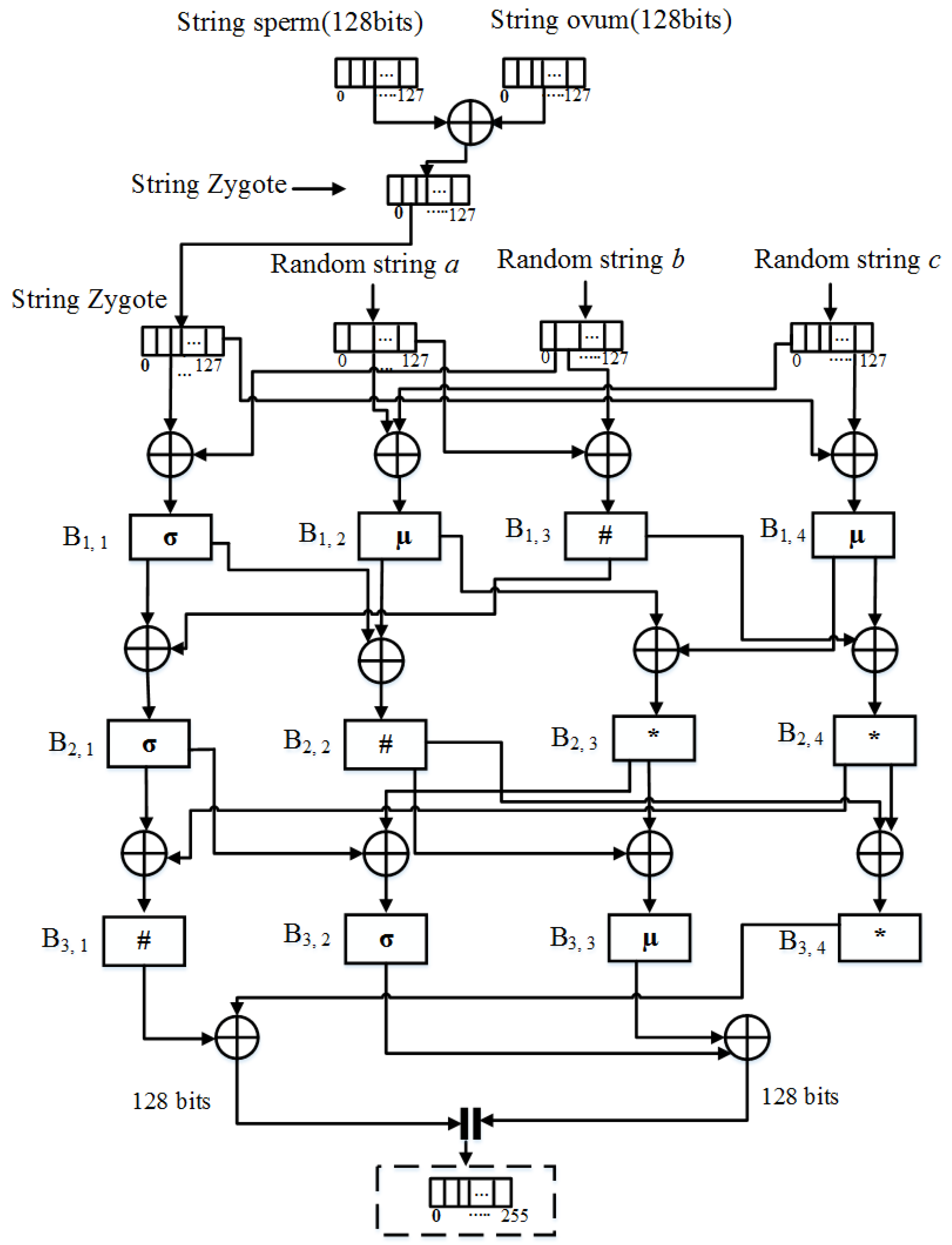
Applied Sciences | Free Full-Text | Omega Network Pseudorandom Key Generation Based on DNA Cryptography
GitHub - joe-darkmatter/node-red-contrib-aes-128-cbc: A hex string-based 128 -bit AES with specifically CBC mode of operation ciphering algorithm for Node-Red module

An example of a 36-character string depicting a 128-bit binary value in... | Download Scientific Diagram

Igor's Tip of the Week #128: Strings list - Malware Analysis - Malware Analysis, News and Indicators

An example of a 36-character string depicting a 128-bit binary value in... | Download Scientific Diagram

![java - String vs char[] - Stack Overflow java - String vs char[] - Stack Overflow](https://i.stack.imgur.com/WhEBr.png)